Spam, scams, and robocalls don’t happen by accident; they’re fueled by data. Data brokers collect, combine, and sell personal information at scale. Scammers and spammers often use that information to target people with unwanted calls, texts, and other attacks.
This article shows how data brokers make scams and spam possible. It also explains the data they use, what can happen because of it, and how you can protect yourself.
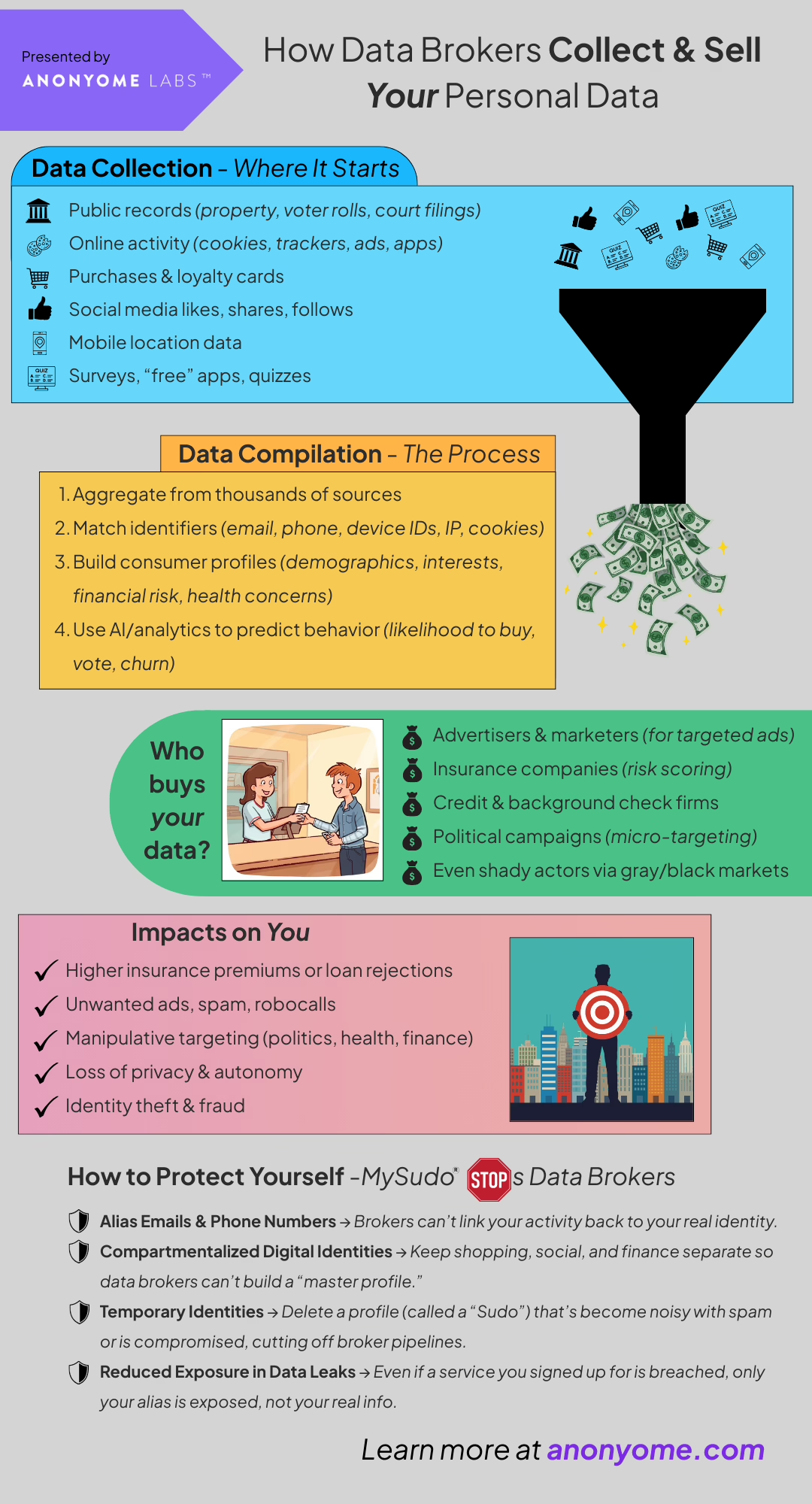
Checkout our infographic on how data brokers collect and sell your data. Learn about their process and ways that you can protect yourself online.
Data brokers pull information from many sources. Data brokers pull information from many sources. These include public records like property and voter rolls, commercial data such as loyalty cards, and purchase histories.
They also collect data from mobile apps, social media, and web trackers. Data brokers don’t just store basic contact details.
They also include guessed information, such as household income, political views, age group, and recent life events. This can be things like having a new baby or moving. They also consider how likely someone is to buy certain products.
Brokers segment people into categories and assign scores (e.g., propensity to purchase, credit risk). This allows buyers to target specific groups. For example, they can reach people aged 30 to 45 who recently moved and are likely to refinance. People often use these lists for mortgage robocalls or phishing attempts.
Aggregated lists get sold or licensed to marketing firms, lead-generators, and sometimes less-scrupulous actors. Those buyers often resell or combine the lists. This multiplies their reach and makes it hard to track who ultimately uses the data.
Telemarketing platforms and robocall services integrate with these lists. Add an auto-dialer or SMS blast, and you can call tens of thousands of high-value targets for a small cost. Automation also lets scammers test different scripts and phone numbers quickly. They can see what works best and adjust their campaigns in near real time.

Actionable checklist
(one minute)