August 8-11 saw the 27th installment of the DEF CON , the largest and arguably the world’s best hacker conference. DEF CON brings together an eclectic community of professionals and enthusiasts across hacking, security, privacy and anything in that neighborhood. DEF CON is temporally and geographically located right near BlackHat and BSides Las Vegas for all looking for an intensive week of high quality material. Here’s what caught my attention.
If you’ve never been to DEF CON
The first thing to need to know about DEF CON is that it is one of the most inclusive conferences I have been to. All stereotypes imagined for hackers, infosec workers and privacy warriors will be simultaneously met and shattered. The army of volunteers are strong in voice and ensure that the masses can move as smoothly as possible. First time speakers are celebrated with warm applause from the audience and a shot of their choosing from the room coordinator.
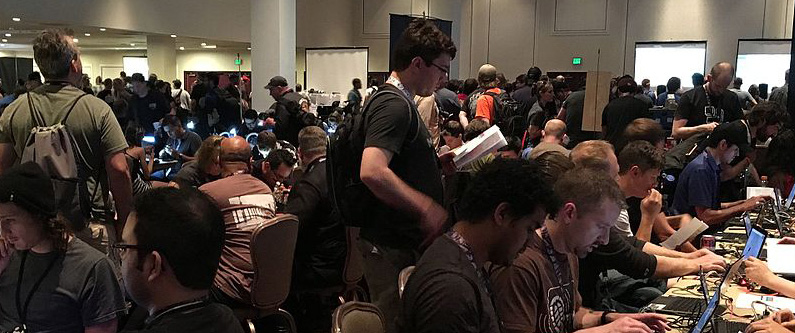
The second thing you need to know about DEF CON is that it is enormous! It’s difficult to bump into a colleague or associate unless you coordinate. This year, DEF CON 27 was spread across four conference hotels for the first time – Paris, Bally’s Flamingo and Planet Hollywood. That speaks highly to the reputation of the event and its material but does make it challenging to move between content streams. As well as main presentation streams, which serve many thousands of people per room, there are also:
- 40+ “villages” focused on specific areas such as Crypto and Privacy, Bio Hacking and Social Engineering. The villages have smaller rooms and it’s typically easier to ask questions of the presenters due to the more intimate setting.
- Contests
- Workshops
- Demo Labs
- Vendor Area
The Vendor Area is quite different to BlackHat, for example. At DEF CON, the vendors offer resources for hackers, penetration testers and the like, and products are available for sale. You won’t see enterprise security vendors exhibiting here, eager to collect your personal data in exchange for a T-shirt or pair of socks.
The third thing you need to know about DEF CON is the diversity of the presentations. You will find presentations covering hardware, software, cloud, mobile, industrial control systems, public policy, law, ethics. Some presentations have an academic focus, others are very applied examples of vulnerabilities that can lead to remote code execution and data exfiltration.
Lastly, you’ve got to remember the 3-2-1 rule. Each day, it’s recommended you have at least 3 hours of sleep, at least 2 meals a day and at least 1 shower!
2019 Highlights
Oh boy, where do I start… so many good sessions. Here are a few things that I enjoyed:
- Are Quantum Computers Really A Threat To Cryptography? A Practical Overview Of Current State-Of-The-Art Techniques With Some Interesting Surprises
- Behind the Scenes: The Industry of Social Media Manipulation Driven by Malware
- API-Induced SSRF: How Apple Pay Scattered Vulnerabilities Across the Web
- Can You Track Me Now? Why The Phone Companies Are Such A Privacy Disaster
- Information Security in the Public Interest
- Hacking Your Thoughts—Batman Forever meets Black Mirror
And here are some events I didn’t get to attend but wished I was able:
- The Tor Censorship Arms Race: The Next Chapter
- Surveillance Detection Scout—Your Lookout on Autopilot
- How You Can Buy AT&T, T-Mobile, and Sprint Real-Time Location Data on the Black Market
- Your Secret Files Are Mine: Bug Finding And Exploit Techniques On File Transfer App Of All Top Android Vendors
I also wish I could have cloned myself and send copies of me around the villages. There is so much good content all over DEF CON!
Conclusion
In general, I am constantly impressed by the ingenuity of a demonstrated exploit and challenged to think differently by the content on human factors, policy and ethics. I am also reminded of the challenge in protecting Anonyome, the Sudo Platform and the data of our MySudo users.
I’ve been to a few DEF CONs now, though I am far from a veteran. I hope to be back next year.