By Dr Paul Ashley, co-CEO and CTO, Anonyome Labs
This article was originally published in Michael Bazzell’s Unredacted magazine, June 2022. To learn more, view the latest issue.
Over the past year or so, interest in decentralized identity (also called self-sovereign identity) has surged. We’ve seen new decentralized identity blockchains created, decentralized identity companies acquired, and various real-world decentralized identity-based projects progressed.
You might ask then, what is decentralized identity? Definitions vary, but this is a good one:
Decentralized identity is an approach to identity and access management (IAM) that seeks ways to allow individuals to manage their own personally identifiable information (PII) instead of using a central authority. An important goal of decentralized identity is to create standards that will allow internet users to control which applications and services can have access to specific types of PII.
Let’s break it down. This definition has three important concepts:
- Identity and access management (IAM)
- User control of their personal information (PII)
- Standards
Identity and Access Management (IAM)
Identity and access management refers to the way you access an online service, such as a website or social media site. The first type of IAM model implemented, and the most common, is centralized. We all know this approach since it involves creating an account on a service. Typically, when you create an account you give the site a username, password, perhaps set up two-factor authentication (2FA) and give other personal information such as your mobile phone number, email address, and credit card information. When I look into my own 1Password app, I see I have more than 200 accounts that fit this model.
The second type of IAM model implemented is also a centralized model but is called federated. In a federated model, you create an account at a central site, such as Google, Facebook, Twitter, LinkedIn or one of the other big sites. When you go to other websites, you might be offered the option of doing a social login such as “Login with Facebook”, where you use your Facebook login to access the third-party site. This type of model relies on sophisticated federation protocols such as OpenIDConnect. The advantage for you is convenience.
Decentralized identity flips these centralized IAM models on their head. With decentralized identity technology, instead of entering a username and password or doing a social login, you would create your own identity in an identity wallet. You would bring that identity to the website or service and create a peer (also called a pairwise) connection with that service. The advantage of creating the connection is that it allows for end-to-end encrypted communication, strong authentication and so on.
Now let’s consider the second part of the definition: user control of their personal information (PII). In my view, the two centralized IAM models are designed to behave exactly opposite to this goal. Those models encourage you to disclose as much of your personal information as possible and collect even more by surveilling your activities covertly. This is particularly bad with social login, where you are actually helping the central site (e.g. Google) to get a broader view of your behavior.
While it’s tempting to hit the social login button to save the bother of creating yet another account and remembering or storing yet another username and password, when you do, you’re really trading your personal information for access and convenience. Unless you carefully consider and agree to the information that the third-party site is asking to access from your social profile (during the initial permissions process, which many people rush through), you can easily expose your personal data, including your gender, age, email address, phone number, relationship status, interests, and even your full list of connections. Almost everything you’ve put into your social accounts could be available to the third-party site owner. This obviously has privacy and security implications.
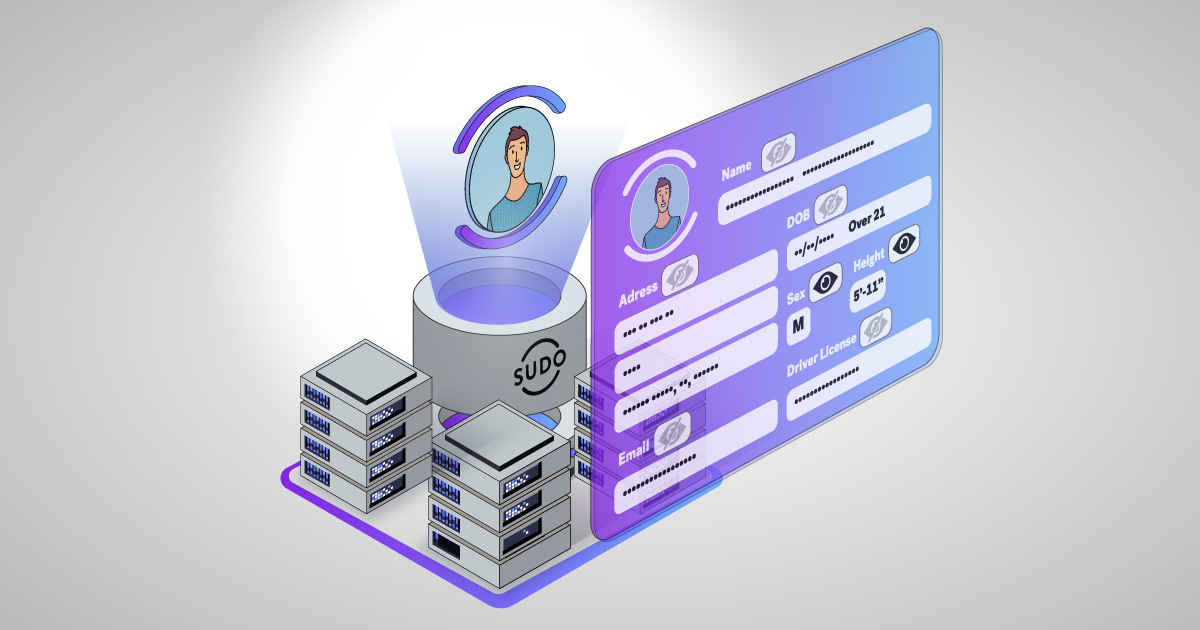
So decentralized identity also flips this broad-ranging data gathering on its head. With decentralized identity technology, you would initially disclose one of your decentralized identifiers (DIDs) to the service to set up a connection. This allows the service to identify you for subsequent accesses and authenticate you using public key cryptography. You no longer need a password. You then negotiate with the service what additional personal information you consent to give to the service. Technology called verifiable credentials (digital documents issued with digital signatures) makes this possible.
Let’s now look at the third important concept in the definition: standards. Arguably the most important goal of the decentralized identity community is to define a set of standards to allow interoperability for users and services—essentially, an interoperable decentralized identity ecosystem. The standards being defined are at standards bodies such as World Wide Web Consortium (W3C), Linux Foundation (Hyperledger and TrustoverIP), and Decentralized Identity Foundation (DIF).
Now we have touched on the high level concepts, let’s dig a bit deeper into the decentralized identity technology.
Identity Wallet

As the user, your view into decentralized identity is via an identity wallet. The wallet allows you to create your decentralized identities and connections with other users and services, and to receive, hold and present verifiable credentials (your digitally signed digital documents).
First, you need to get an identity wallet. There are a few different ones out there; one example is the Lissi wallet (lissi.id/mobile), which is a mobile application purposely built to allow the user to participate in a decentralized identity world.
The wallet is designed to hide much of the complexity of decentralized identity, but let’s cover some detail here. When you create your first decentralized identity, you are in fact creating a private/public key pair (usually based on Elliptic Curves, e.g. ec25519) and a unique identifier called a DID. A DID is a simple text string consisting of multiple parts:
did:indy:sovrin:7Tqg6BwSSWapxgUDm9KKgg
The string above has this meaning: “I am creating my decentralized identity following the Indy DID method, and the identity is anchored on the Sovrin mainnet blockchain.” If you were to provide that DID to a service or another user, it would be resolvable to an address on the Sovrin mainnet where the DIDDoc could be returned. The DIDDoc contains your public key and an address where to reach you.
There is a lot to unpack in that paragraph. Sovrin is a Hyperledger Indy-based blockchain specifically built for decentralized identity. Being a permissioned blockchain, it is a network of validator nodes (twenty four for each of the three Sovrin networks: mainnet, staging, test). It is designed to support decentralized identity-based applications. Anonyome Labs is one of the founding stewards of Sovrin, meaning we have been running a validator node on the Sovrin network for over three years now. Think of a validator like a bitcoin miner.
A blockchain is used for decentralized identity because it provides an anchor for trust. Not only can you write your DIDs to the blockchain, but other parties, such as verifiable credential issuers, can write credentials definitions and their own DIDs (unique identifiers) as well. Because the blockchain is immutable (can never be altered, only added to), there is no way for a hacker to modify the information on the blockchain.
DIDDoc is also important. The DID points to a location on a blockchain so that a DIDDoc can be retrieved. The DIDDoc gives the decentralized identity’s public key (for establishing connections) and an address that can be used to reach you as the user. A well-designed identity wallet shields you from the complex technical information I’ve described. From your perspective, you create your decentralized identity and take it out and use it. Complexities around cryptography, endpoints, and blockchains are not that interesting to the everyday user.
So, to answer the question we started with: can decentralized identity give you greater control of your online identity? Clearly yes.
I’ll leave it there for now. This is the first in a series of articles on decentralized identity from Anonyome Labs. In future articles I’ll discuss:
- Decentralized identity focused blockchains
- Decentralized identity verifiable credentials
- Identity (data) hub concept
- Real world projects leveraging decentralized identity
- The key decentralized identity standards, and more.
Update:
Anonyome Labs is building a set of SDKs for Sudo Platform so our enterprise customers can quickly create their own digital identity wallet. We also plan on building an unbranded identity wallet app if an enterprise customer wants to get to market faster.