Trusting Digital Identity
The modern web provides users with instantaneous access to information and a wide range of digital capabilities never before seen in the world. People are able to send electronic communications, make remote purchases for rapid delivery, and access the worlds knowledge and information via their electronic devices. Online users can perform sensitive functions, such as communicating with their doctor, ordering prescription medication, conducting financial transactions, and shopping online.
It has been observed that the internet was created without an identity layer. This unforeseen necessity has left online content and service providers to provide user accounts and security methods (e.g., username and password) they created themselves. Users, not wanting to remember numerous passwords, often reuse their login credentials. This leaves people vulnerable to cyberattacks and account compromises. Federated account management (e.g. “Login With ___”) services have tried to help, but left users beholden to account providers that have incentives to monitor internet activity.
Since issuing identity cards has traditionally been the role of the state, governments have entered the digital identity arena in order to provide secure digital credentials for their citizens.
Government’s Traditional Role in Identity
Every individual is unique and their identity comes by virtue of their birth, family, and social environment. When social environments are small, it is easy for everyone to know each other. However, as social environments grow into much larger cities and there is a lot of interaction between geographically dispersed groups, knowing someone by sight becomes impossible.
Governments have been created in societies to help people interact in a mutually agreeable fashion. As part of this process, it fell on governments to help people to be able to identify each other also in a mutually agreeable way. This led to identity papers being issued by governments, so that individuals could present them when needing to establish a level of trust between parties who don’t know each other.
While that type of identity paradigm benefits society in many ways, it can also leave people beholden to the government. If that sounds strange, anyone who has stood in long and tedious lines at the local Department of Motor Vehicles can sympathize. However, the real drawback of the model where governments provide identity methods is that governments can also take away those credentials, which happens when someone moves between states and must surrender their existing identity card.
Digital Identity
With traditional physical identity cards, proving one’s identity is largely transactional (e.g., show a card to get into a building) without a means of re-verifying the card’s ongoing validity. Conversely, digital identity enables a wide range of previously impossible scenarios, such as immediate cryptographic verification. This process helps store clerks from being fooled by look-a-like fake IDs.
The cryptographic verifiability properties of digital identity also help people prove their identity online while visiting remote websites and also helps web service operators to be assured that visitors are who they claim to be. This helps facilitate everyday activities, such as online purchasing or checking email. However, it also enables more sensitive activities, such as patient-doctor communications, online banking, filing income taxes, purchasing securities, etc.
While government backed digital identity delivers a high degree of trust to all parties of identity transactions, it also leaves people with an increasing dependency on the government issuers. Since digital identity creates the ability to conduct medical, financial, social, commercial, personal, etc. activities online, any kind of disruption to that identity now becomes catastrophic to consumers. Such disruptions can happen after forgetting to renew a driver’s license, due to random administrative issues, identity service (internet) disruption, or from a cyberattack.
If people use their government issued digital ID for their online activities, any disruption to that ID can leave them unable to function online.
Utah’s “State Endorsed Digital Identity”
The US state of Utah is taking a novel approach to digital identity – one that leaves people with more control. Utah’s approach draws from the time-honored birth certificate process.
When a baby is born, the parents choose their child’s name and that becomes the means by which they are known throughout their life. The child’s name wasn’t selected or assigned by the government, rather it came from the parents. However, since the government provides a trusted identity service, the child will also need a credential in the form of a birth certificate. Birth certificates provide a government-backed representation of a person’s name and other vital information … all of which was provided by the parents.
Passed into law in 2025, Section 1202 of the Utah Code reads:
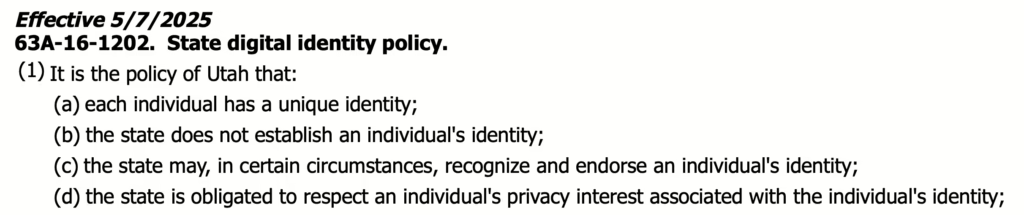
Using the birth certificate paradigm as its model, Utah has asserted that each individual has a unique identity, which is not established by the state, but is inherent to the individual. In a world where governments typically issue a person’s identity credential (e.g., driver’s license or passport), Utah made the choice to affirm individuality and then to endorse it. This is why Utah’s new digital identity system is known as the State Endorsed Digital Identity (SEDI).
How a SEDI Credential Works
While the exact technology stack for SEDI has yet to be announced, at its technological base, SEDI will generally draw from a Decentralized Identity (DI) paradigm. In DI, a user creates their own unique cryptographic identifier called a Decentralized Identifier (DID) using an app they control. DIDs are like web addresses (i.e., URLs) and that reference both a unique identifier and set of cryptographic public keys. DIDs provide the basis for establishing secure communications, encrypting files, and utilizing verifiable credentials.
Using the DI paradigm, a user will present their DID to the state along with other traditional identification, such as a birth certificate, driver’s license, or other identity documents the state deems trustworthy and chooses to accept. The following figure illustrates the basic interactions between the user and the state when requesting a SEDI endorsement credential:
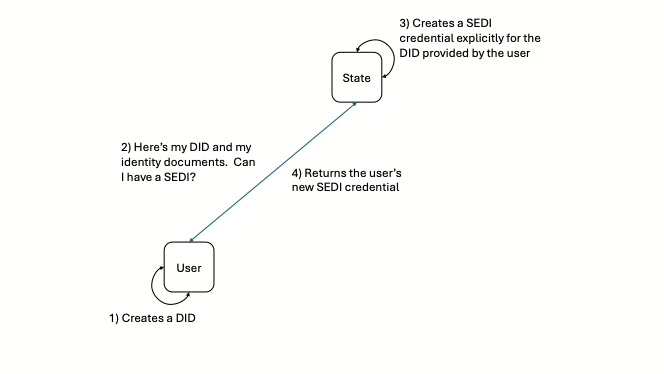
Using this process, a person will create a DID (that they alone maintain and control) using a SEDI-enabled wallet application. It is important to note that the DID is theirs forever and while the state can issue a SEDI credential to the user tied to their DID, the state does not take possession of or control the DID, itself.
That is what is unique about SEDI’s use of the DI paradigm. The user can continue to use that same DID for receiving other credentials from other sources and may perform many other DI functions. If the SEDI endorsement is ever revoked, the user still keeps the original DID and may continue to use it however they choose. This process of issuing SEDI credentials tied to a person’s unique DID identifier enables them to keep the anchor DID even if the SEDI endorsement credential were ever revoked for any reason.
Using a SEDI
Once a person receives their SEDI credential, they can use it to perform a wide range of digital activities, such as identifying themselves to and conducting business with the state. This enables them to securely prove their identity without the need for a username or password, to secure digital communication channels, cryptographically sign documents, make requests, etc. Once implemented, users will be able to securely pay taxes, renew drivers licenses, obtain a hunting or fishing license, etc. either in person or online.
As SEDI becomes adopted by the internet industry, users will be able to do more than conduct business with the state government. Users will be able to login to websites, remit payments, make verified online purchases, enroll in social media, prove their age as required, etc.
Types of SEDI Assertions
Utah Code Section 63A-16-12-1202 discusses several security and privacy requirements for SEDI usage both in and potentially outside of primary government environments. SEDI-enabled technologies should implement specific functionality outlined in Utah State Code.
Selective Disclosure
Paragraph (1)(g)(i) of Utah Code states that a SEDI holder is entitled to choose “how” and “to whom” “the individual discloses the individual’s state-endorsed digital identity”, which is interpreted to include both in-government and outside of government usage scenarios. This paragraph further entitles users to determine “which elements” they choose to disclose, which is referred to within the identity industry as Selective Disclosure.
The following figure illustrates three Selective Disclosure use case scenarios in which a person may elect to disclose all or some of their SEDI-related personal information.
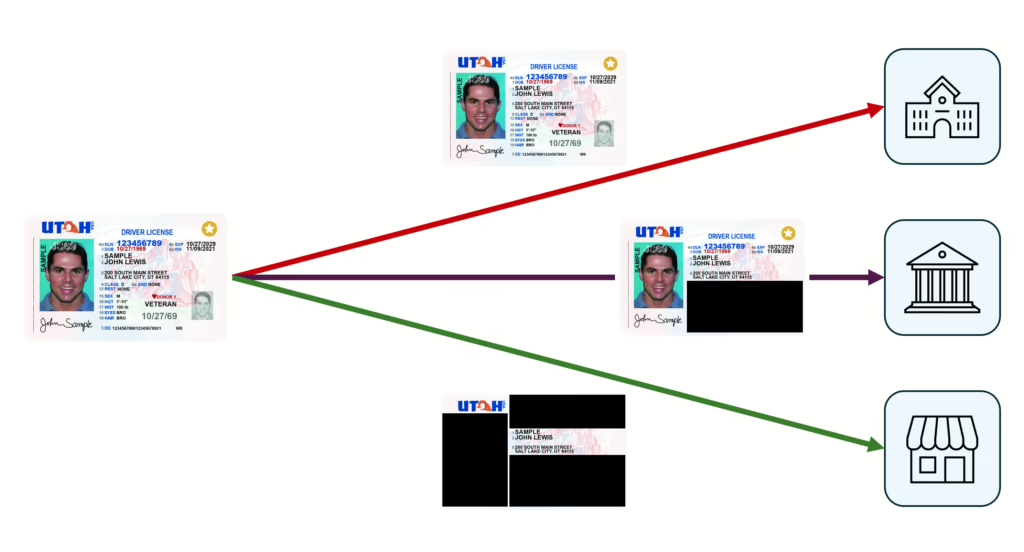
When presenting their SEDI to the state’s Department of Motor Vehicles (DMV), it is presumed that the DMV already has their full identity information set, so it is not necessary to hide or mask any of that information through Selective Disclosure. However, when presenting a SEDI to a bank, only the primary identity information is required, so the user is able to avoid divulging physical attributes, veteran status, donor status, etc. as depicted above. Finally, if a person is interacting with a business to prove their name and address, SEDI’s Selective Disclosure functionality enables them to share only that information while not having to disclose any other information contained within the SEDI credential.
These Selective Disclosure features are a significant privacy advancement above current identity proving methods (e.g., providing a photo of their driver’s license) which typically only enable users to prove their identity after they provide all information contained within the credential type. While current methods result in verifiers (e.g., businesses or web services) collecting vast amounts of irrelevant personal data, SEDI dramatically enhances personal privacy by enabling users to provide only the specific personal data items that are necessary.
Age Range Disclosure
From the Utah Code cited above, paragraph (2) further provides personal data protections, such as:
“The state may not endorse an individual’s digital identity unless:” (2)(e) “the state-endorsed digital identity enables an individual to” (2)(e)(i) “selectively disclose” and (2)(e)(ii) “verify that the individual’s age satisfies an age requirement without revealing the individual’s age or date of birth”.
On the surface, one might assume that the age requirement could simply be embedded in a SEDI as “over age 18” or “over age 21”, as was done in the Mobile Driver’s License (i.e., mDL; ISO/IEC 18013) standards. However, this is impractical given the numerous varying age requirements throughout both government and society. As an example, US military recruits must be at least age 17 to join the US military. In Utah, to run for legislative office, candidates must be at least age 25 or at least age 30 to run for Governor. Utah State Code stipulates specific employer work requirements based on age ranges, such as 14-15, 16-17, 18, etc. Given the wide variety of cases where age must be proven “without revealing the individual’s age or date of birth”, simply including a series of “over age XX” fields in the SEDI credential is impractical.
The age range disclosure functionality provided by SEDI helps users maintain their privacy by limiting disclosures to “meets requirements” instead of divulging specific identity data elements. There are several technology-based solutions by which to express a data item or range of data items without revealing the data items themselves. A cryptographic digital signature type, known as a Zero Knowledge Proof (ZKP), can be used to enable this privacy-preserving data proving capability.
SEDI Protects Against Unwanted Surveillance
From Utah Code Section 63A-16-12-1202, paragraph (2)(d) stipulates protections for SEDI holders as:
“(d) the state ensures that when an individual uses a state-endorsed digital identity
…
(ii) “the use is free from surveillance, visibility, tracking, or monitoring by any other governmental entity or person”.
Modern methods for tracking individuals in digital settings have become significantly advanced with the advent of targeted advertising. Most tracking methods perform a combination of data collection analysis and individual tracking identifier correlation. Tracking identifiers can take the form of anything that uniquely identifies a person, such as cell phone number, email address, social security account number, driver’s license, etc.
In digital environments, even static or semi-permanent Decentralized Identifiers (DIDs) can also contribute to surveilling users’ activities. None of these tracking methods should be used without specific consent from the user. In order to accept a SEDI credential, verifiers will need to support surveillance protections required by Utah state law. Keeping users free from unwanted surveillance is an important step forward.
SEDI: A Model for Privacy-Enhancing Credentials
According to Utah’s official State-Endorsed Digital Identity whitepaper (Oct 2025), the basic principles governing SEDI are:
- Comprehensive Legal Framework – clear governance, specific requirements, enforceable standards, open standards, explicit transparency, and separation of duties
- Individual Control – individual create and maintain perpetual control of their core identifier upon which the SEDI endorsement is based
- Privacy – implemented using a decentralized, peer-to-peer approach where individuals control their SEDI elements and are free from surveillance tracking
- Parental Rights and Delegation – SEDI outlines a series of parental rights to enable parents to manage their children’s digital identity and to provide tools to parents that keep their children safe from exploitation or identity misuse
- Critical Public Infrastructure and Security – in the modern era given the significant value of personal data, SEDI recognizes the digital identity ecosystem as a critical infrastructure to be protected similar to how other critical infrastructures are protected
- Backwards compatibility – SEDI maintains backward compatibility with existing digital identity ecosystems in order to ensure that SEDI holders may continue to interact with such ecosystems while participants transition to the more secure and private SEDI architecture
Utah has taken a very progressive and forward-thinking approach to government-endorsed digital identity that is intended to position the information and privacy rights of individuals ahead of the needs (current or future) of the state or commercial enterprise. Given the amount of personal data surveillance, collection, and aggregation happening on today’s internet, Utah’s move is a much needed and welcome approach. It is foreseen that Utah’s SEDI model will become a pattern by which other governments may create and issue secure and private digital identity for their citizens.