Introduction: Privacy Starts with Separation
Most privacy advice focuses on hiding your activity. But modern tracking doesn’t depend on visibility alone—it depends on connection. If your activity can be linked together, it can be tracked. To truly reduce tracking, you need to prevent those connections from forming in the first place.
Identity linking is the process of connecting different pieces of your activity into a single profile. This happens when you reuse:
Across platforms and contexts.
Two identifiers are especially powerful:
Phone Number
These become the backbone of identity linking.
Instead of using one identity everywhere, create separate identities for different contexts.
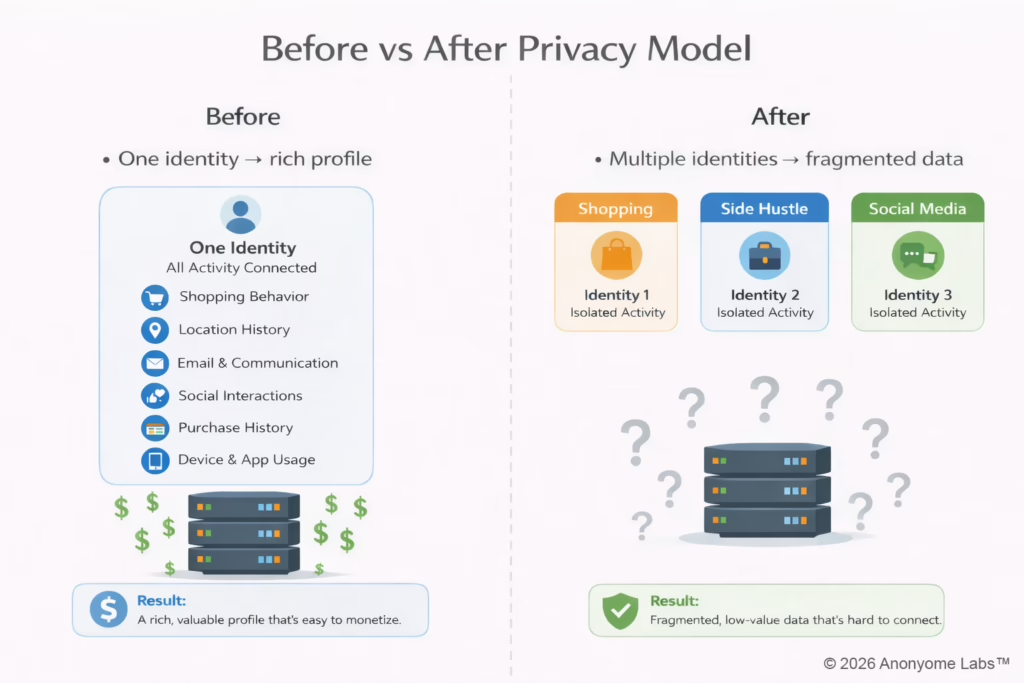
When identities are separated:
Instead of one rich profile, you create multiple fragmented ones. Privacy doesn’t come from hiding, it comes from separation.
Managing multiple identities manually is difficult. MySudo®, which is designed for identity separation, make it easier by allowing you to:
This enables:
You can’t fully stop companies from collecting data. But you can stop them from connecting it. And when the connections break, the system loses its power.