It’s not just ads…It’s your identity
Most people think ad tracking is about cookies and annoying ads. In reality, it’s something much more powerful—and much harder to escape.
Behind the scenes, companies are:
This is why even after you:
…you still see eerily relevant ads. Because ad tracking isn’t just about tracking activity—it’s about tracking identity.
Ad tracking works by collecting small pieces of information and combining them into a larger picture. Here are the main ways it happens:
Cookies are small files stored in your browser that track:
There are two main types:
These allow companies to follow your activity across the web.
Even without cookies, your device can be identified using:
Combined, these create a unique “fingerprint”. Unlike cookies, you can’t easily delete or block this.
When you open emails, companies can track:
This is often done using invisible tracking pixels. Your email becomes a persistent identifier tied to your behavior.
Your phone number is one of the strongest identifiers you have. It’s often used to:
Once your number is connected, it becomes a backbone for tracking.
Companies don’t just track one device; they track all of them. They connect your:
Using shared signals like:
This creates a unified view of your activity across devices.
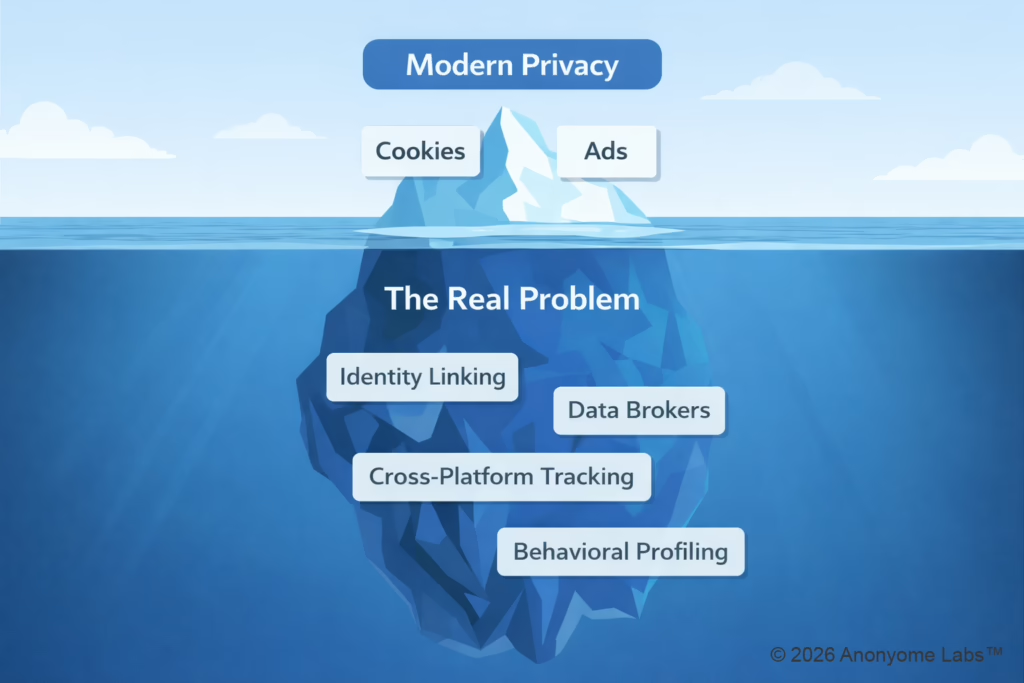
Each of these methods alone is useful. But the real power comes from combining them. This process is called identity linking or identity stitching.
Here’s how it works:
Now everything is connected.
All tied to a single identity.
Most privacy tools focus on blocking individual tracking methods. But identity stitching bypasses that.
Even if you:
As long as your identity stays consistent, tracking can rebuild itself.
Ad tracking has evolved. It’s no longer just about:
It’s about:
That shift changes everything. Because instead of tracking sessions, companies now track:
When everything is connected:
And that data doesn’t just stay in one place. It’s:
Often without your knowledge.
The entire tracking system depends on one thing…a consistent identity across contexts. If that identity stays intact:
But if that identity is broken apart the system loses its power.
To actually reduce tracking, you need to do more than block signals. You need to prevent your identity from being connected in the first place. That’s where: